TLDR: We are seeing cyber breaches in the news daily. We all know it is happening and nobody is an exception to a potential attack. Here’s how we ensure our customer’s data is safe.
Your information is important, not only to you, but to us.
If you are an ASE Trust customer, you can rest assured that your data is already protected on the dark web by us. As part of our service, you can leverage the broadest and deepest coverage of dark web sources to gain visibility into threat actors and their activities.
Our service accesses restricted channels and automate intelligence gathering to anticipate attacks targeting your organisation, employees, and customers. When we get notified of your details appearing on the dark web, we notify you and take steps to make sure your information is protected.
You have taken steps to protected yourself against malware, you’ve even taken precautions for a direct exploitation. But what have you done to protect your organization against its greatest asset, your staff?
We all have them, the click-everywhere, download-anything, user:password1 (written on a post-it) team members. Your colleagues and team (as great as they are) are the weakest links in the security chain.
Over 60% of confirmed data breaches leveraged weak, default, or stolen passwords.
Yes, those include your sister’s name with a number after it. Security training with your team is a fantastic way to start lowering the potential threat.
It’s clear detecting the use of compromised credentials should be a top priority for any security team.
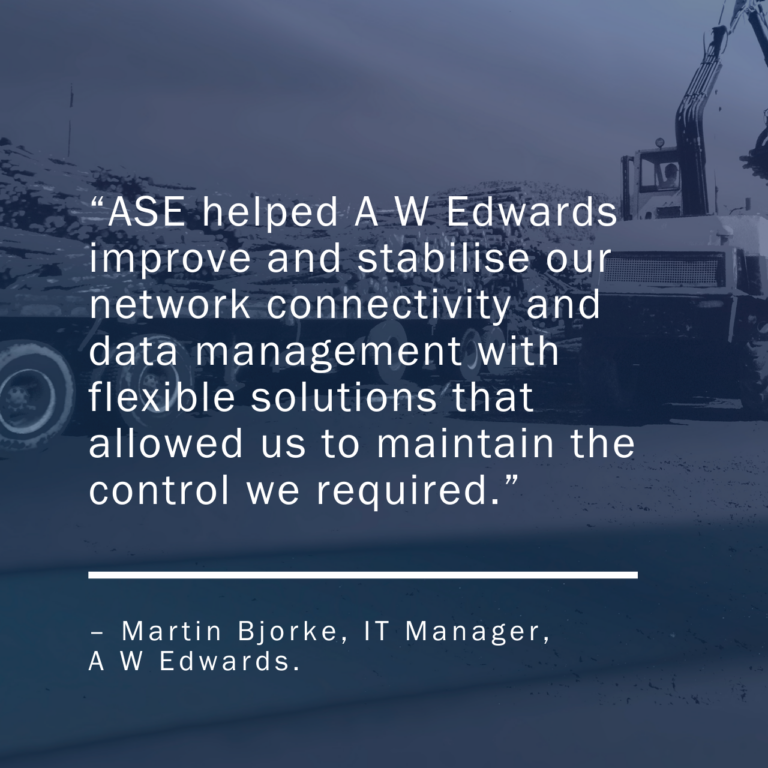
Whether you’re seeking technology solutions to detect this attacker technique or an expert team to detect it in your environment, ASE has your back with our Trust product.
Talk to our team today about keeping your data secure.
PS. Optus Customers, book your free security check NOW